Cardano’s Midnight Network: Passive Income and Investment Outlook for 2026
Midnight is a Cardano‑linked blockchain that uses zero‑knowledge selective disclosure to keep smart‑contract inputs private while enabling auditable proofs. Its NIGHT/DUST token split is designed to separate governance from usage and appeal to regulated, enterprise use cases.
- Compliance‑friendly privacy: ZK selective disclosure enables app‑level confidentiality with verifiable proofs, targeting identity, finance, and enterprise workflows.
- Two‑token economics: NIGHT is tradable and generates nontransferable DUST for fees, decoupling governance/stake from transaction costs to stabilize usage.
- Investment signals & risks: Staking offers passive yield, but adoption, scheduled token unlocks and regulatory perception will drive mid‑term price outcomes.
Midnight is a privacy-focused blockchain developed by Input Output Global (IOG), the team behind Cardano. In public blockchains, like Solana or Ethereum, most smart contracts expose data by default.
However, Midnight’s design centers on “selective disclosure.” Users can keep sensitive information private while still proving compliance-relevant facts with cryptographic proofs.
This premise allows Midnight to fit into the Privacy Coin crypto narrative that gained a lot of popularity over the past few months.
But is NIGHT token worth investing in?
What Cardano’s Midnight Network Actually Wants to Achieve
Midnight labels itself as a programmable privacy layer. Developers can create apps where some data stays private and other parts remain public and auditable. Midnight relies on zero-knowledge proofs (ZKPs) to validate private computations without revealing inputs.
This differs from older privacy coins that mainly focus on hiding transactions. Midnight targets privacy for smart contracts and business logic. This is important for regulated or data-sensitive categories like identity, institutional finance workflows, and enterprise applications that can’t expose counterparties, balances, or internal rules to the public.
The NIGHT Token Model
Midnight’s token economy splits value and network usage into two components.
- NIGHT is the tradeable token. It is transparent on-chain by design.
- DUST token is used to pay for transactions and smart contract execution.
Holding NIGHT generates DUST over time. Users spend DUST to use the network, and DUST replenishes based on the user’s NIGHT balance. DUST cannot be transferred, and it has no separate market.
This model tries to fix two issues seen on many chains:
- Unpredictable gas costs. If your usage depends on a token you must buy constantly, fees can become volatile. Midnight tries to make usage more predictable for long-term holders.
- Users “spending” their governance stake. If transaction fees require the same token used for governance or staking, heavy network users gradually reduce their influence. Midnight separates these roles.
 DON’T GET REKT
DON’T GET REKT
Curated drops, testnets and red flag alerts straight to your inbox ✌️
What Makes Midnight Different From Other Privacy Networks
Midnight’s main differentiation is “compliance-friendly privacy.”
- NIGHT stays transparent. That helps with exchange listings and custody, since the base asset does not function as an anonymous value-transfer coin.
- Privacy lives in the execution layer. ZK proofs protect data in smart contract logic and transactions, while selective disclosure allows users to reveal information when required.
That approach tries to thread a narrow needle. It aims to deliver privacy that enterprises can use without inheriting the regulatory stigma that has hit some privacy coins over the years.
Here’s a comparison of Midnight with other popular privacy networks like Zcash and Monero.
| Feature | Midnight (NIGHT) | Zcash (ZEC) | Monero (XMR) |
| Main purpose | Privacy for apps and smart contracts | Private payments (optional) | Private payments (default) |
| Is privacy mandatory? | No – selective, app-level | No – user chooses | Yes – always on |
| What is private? | App data and contract logic | Transaction details (when shielded) | All transaction details |
| Smart contracts | Yes (privacy-preserving) | No | No |
| Token role | Governance, staking, network access | Payment coin | Payment coin |
| How fees are paid | Using DUST (generated from NIGHT) | Using ZEC | Using XMR |
| Regulatory friendliness | Designed to be compliant | Mixed | Low (frequent delistings) |
| Best suited for | Builders, enterprises, private DeFi | Users wanting optional privacy | Users wanting maximum privacy |
Monero (XMR) fits the classic privacy coin narrative most strongly because privacy is mandatory, on by default, and embedded directly into every transaction. Zcash sits in the middle with optional shielded privacy, while Midnight (NIGHT) is better described as a privacy infrastructure and smart contract network rather than a pure privacy coin.
Passive Income Opportunities With NIGHT in 2026
If you approach NIGHT as a 2026 investment, passive income matters because it can offset volatility and encourage holding rather than short-term trading.
1) Staking and delegation
Midnight uses a proof-of-stake security model. The broad expectation is that NIGHT holders can delegate stake to validators and earn rewards, similar to Cardano’s delegation system.
For most holders, the likely path looks like this:
- Hold NIGHT in a compatible wallet.
- Delegate to a validator (potentially operators experienced from Cardano’s stake pool ecosystem).
- Earn staking rewards in NIGHT.
Key risks remain the same as other PoS networks: reward rates can change, validator performance affects yield, and token price can overshadow the value of rewards.
2) Validator operations
Running infrastructure can generate income, but it fits only operators with technical skills, uptime discipline, and sufficient stake. This route tends to be more competitive and operationally demanding than simple delegation.
3) “Utility yield” via DUST generation
DUST does not create cash yield because you cannot sell it. Still, for builders or frequent users, DUST generation can reduce operating costs. If Midnight adoption increases, a developer holding NIGHT could subsidize user fees by delegating DUST to contracts, enabling smoother onboarding.
This matters because utility that reduces costs can support demand for NIGHT among teams that actually ship products.
Price and Token Supply: What Investors Need to Watch
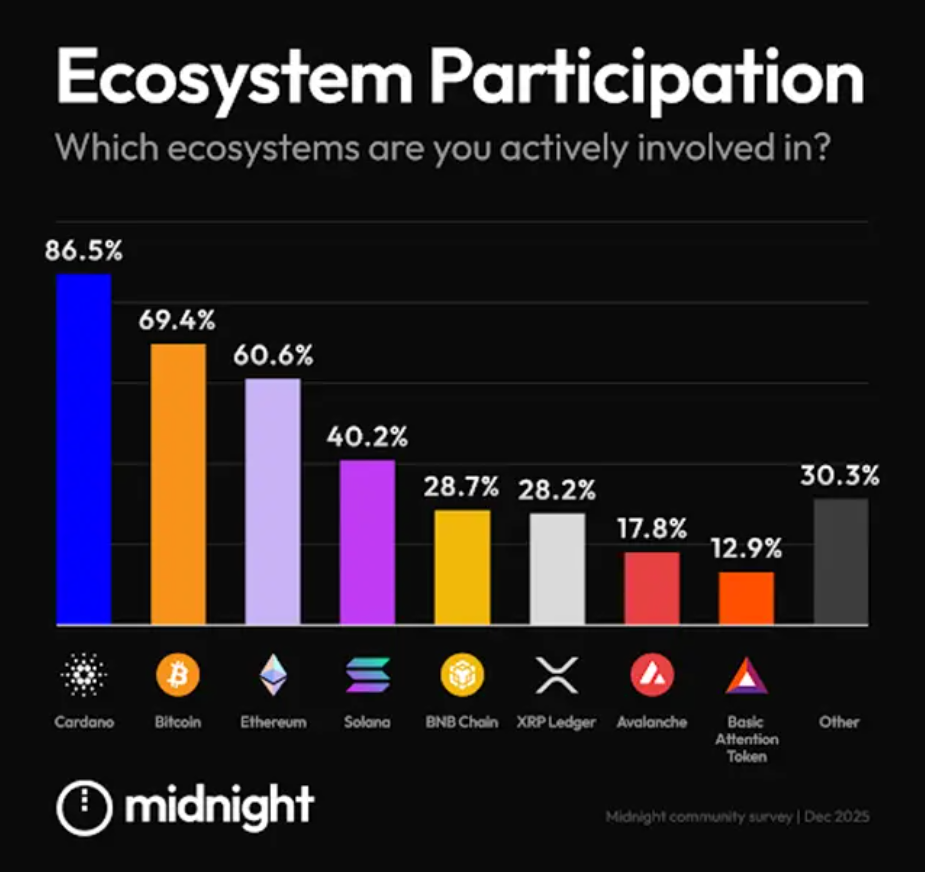
NIGHT’s launch saw sharp volatility. Early price discovery spiked and then corrected hard, which is common for large distributions. The more important factor for 2026 is supply flow.
Midnight distributed tokens widely and implemented a long “thawing” schedule. That reduces the odds of a single cliff unlock, but it does not remove selling pressure. Every scheduled unlock creates a predictable supply event that traders often front-run.
If you consider NIGHT as a 2026 investment, track three things:
- Unlock cadence and circulating supply growth. More liquidity can weigh on price if demand does not keep up.
- Staking participation. High staking rates can reduce liquid float, though it does not eliminate selling.
- Real usage signals. If apps and integrations drive demand for holding NIGHT (for DUST generation and governance), supply unlocks become easier to absorb.
Is NIGHT Worth Investing For 2026?
A practical way to judge NIGHT is to treat it like a “network-rights asset” with optional cash yield from staking.
Reasons it could be attractive in 2026
- Midnight targets a real constraint in public blockchains: confidentiality.
- The two-token model (NIGHT + DUST) offers a coherent design for stable network usage.
- Developer experience looks more approachable than many ZK-first platforms.
- Wide distribution reduces single-entity concentration risk, though exchanges can still concentrate liquidity.
Reasons to stay cautious
- Adoption risk remains high. Privacy infrastructure only matters if developers ship apps people use.
- Token unlocks can create extended sell pressure through 2026.
- Regulatory perception of privacy tech remains uncertain, even with a compliance-friendly design.
- Competition is serious: ZK tooling improves fast, and Ethereum-based privacy systems can move quickly.
If you want passive income exposure, staking will likely be the main route in 2026. If you want fundamental upside, focus less on the privacy narrative and more on adoption milestones, integration progress, and how the market handles scheduled supply unlocks.
We're sorry you did not find what you were looking for. Please select the reason this article was not helpful.